- Flexera Community
- :
- FlexNet Manager
- :
- FlexNet Manager Knowledge Base
- :
- Target a certain network card for Rule executions using mgsipscan
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Mark as New
- Subscribe
- Mute
- Permalink
- Report Inappropriate Content
- Article History
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
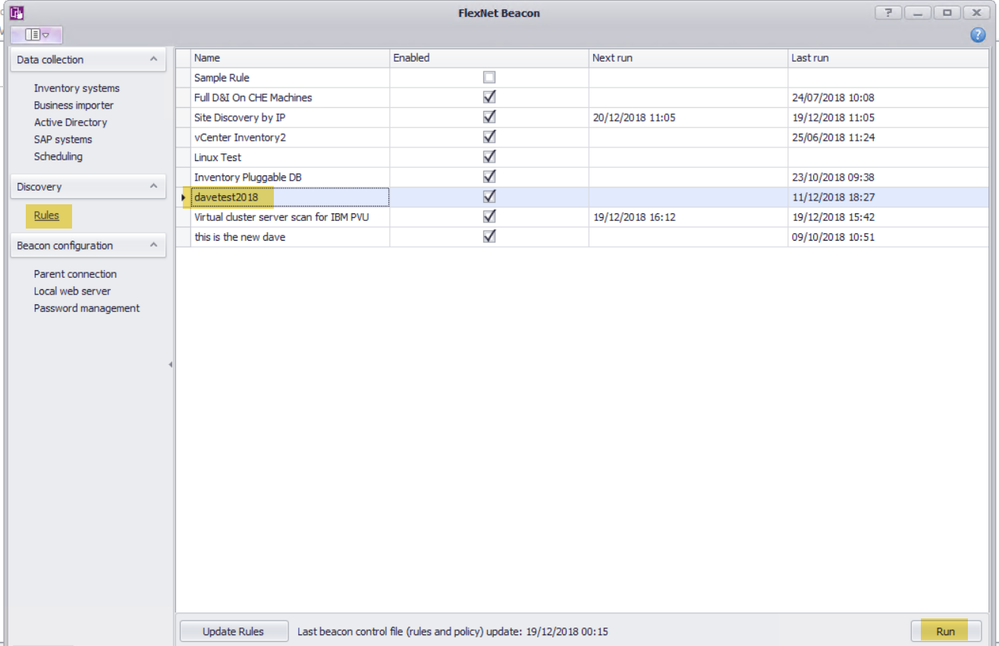
On your beacon rules that can execute (such as VMware rules) using the mgsipscan executable, however, there is no way in the GUI to set which network card you wish for the IPscan tool to actually use. Usually, it will be able to work this out without setting this option but if you have 2 IPs that are the same coming from 2 network cards on your beacon you may need to force what card you wish for mgsipscan to inspect, fortunately, this can be set using the following process:
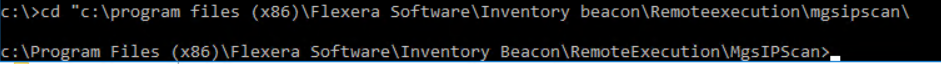
On your beacon, open up an admin cmd terminal and navigate to the following location
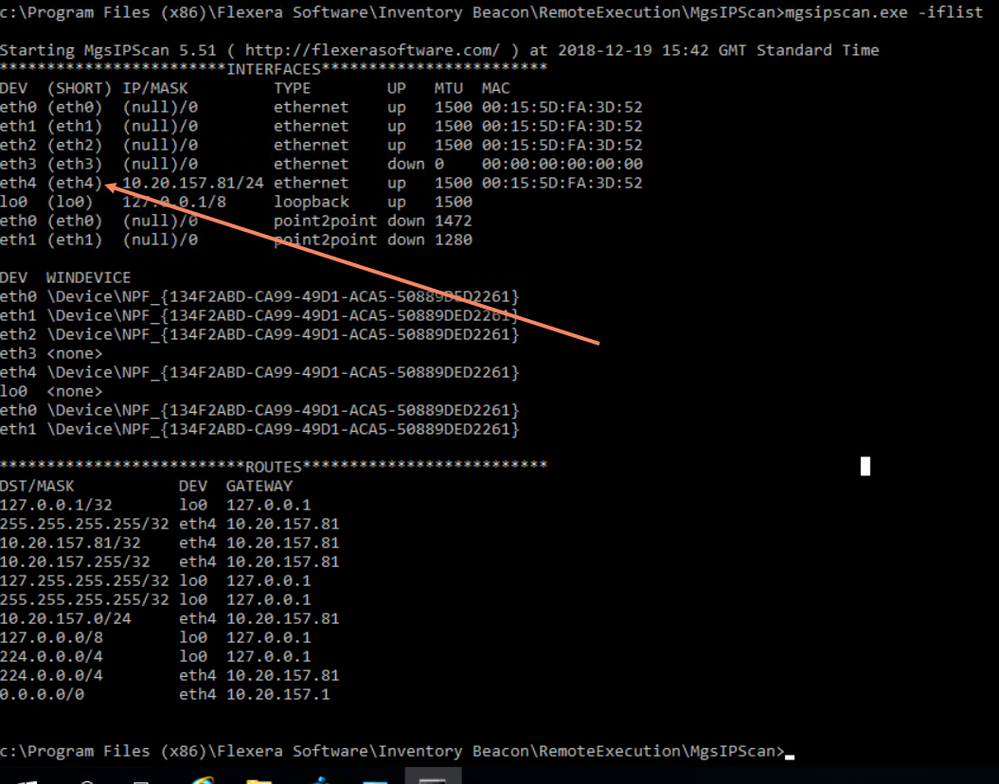
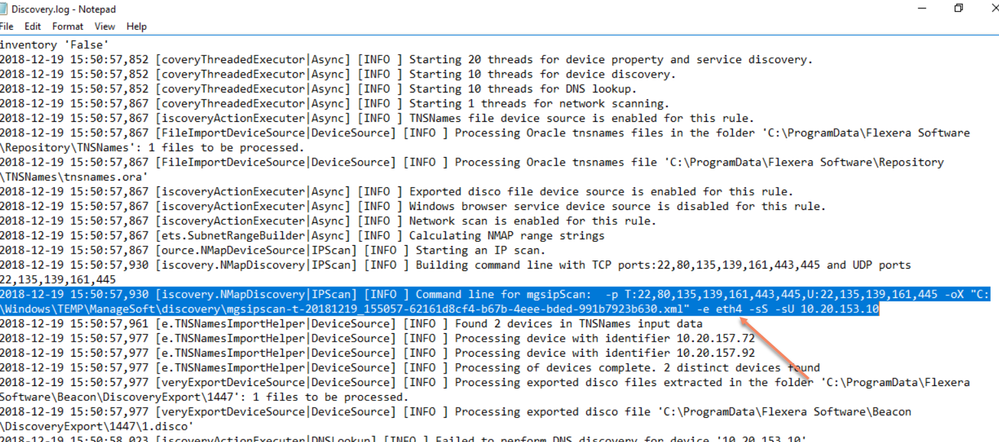
Input: mgsipscan.exe –iflist and make note of your network adapter you with to target, in my case its eth4
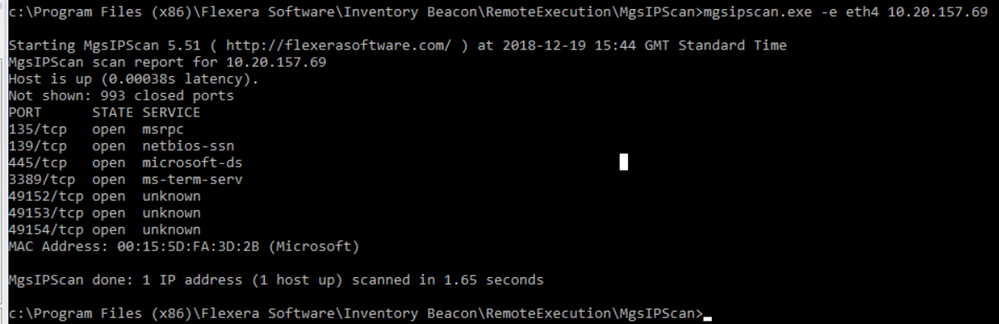
Now do a test against this card with an IP address, in my case I used a client machine for the test
Input: mgsipscan.exe –e eth4 10.20.157.69
(Change IP and network card name as required)
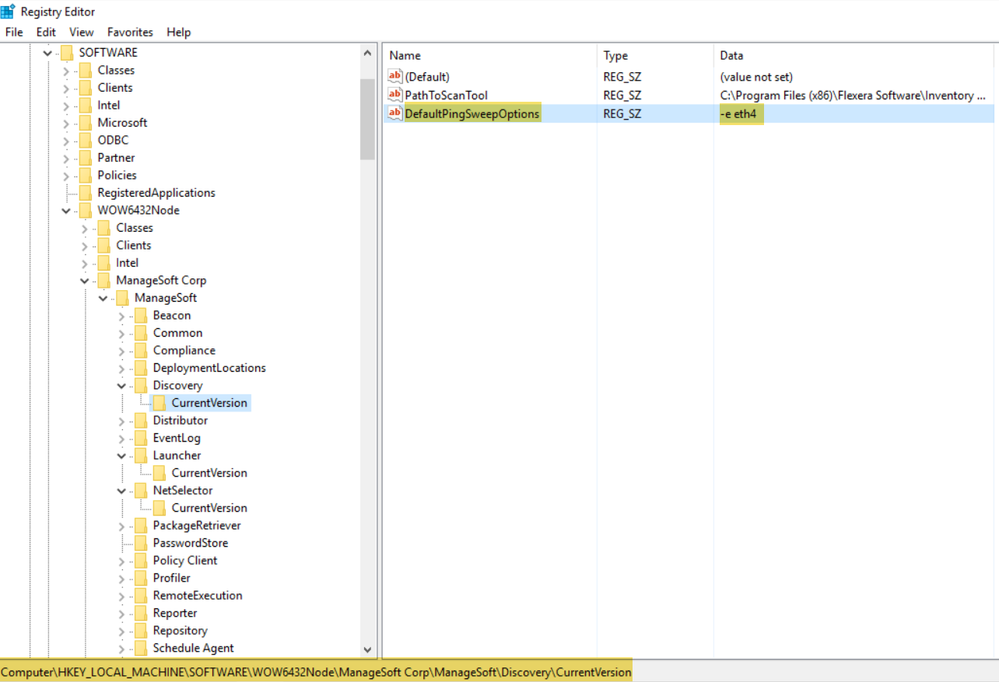
Once we have confirmed as accessible that we can put this into the registry, make a string under
hklm\software\wow6432node\managesoft corp\managesoft\discovery\currentversion
string: defaultpingsweepoptions
value: -e eth4
Navigate to your beacon UI and start off the IP scan rule,
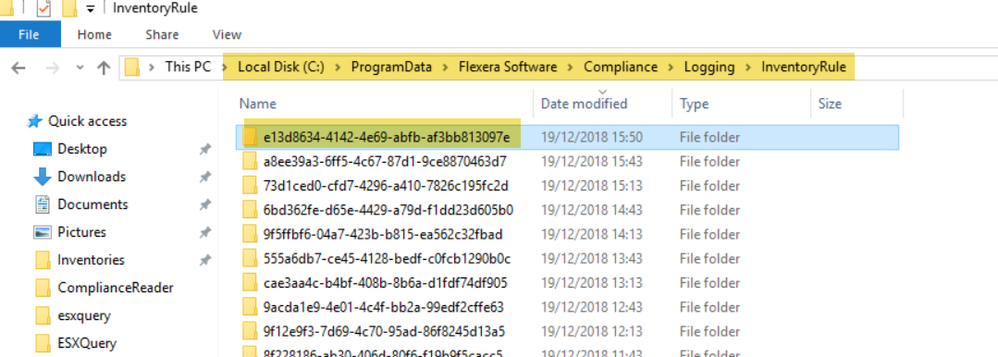
Wait 5 min or so for the rule to complete, then navigate to the path listed below and choose the latest folder in this location, sorting by modified date is useful
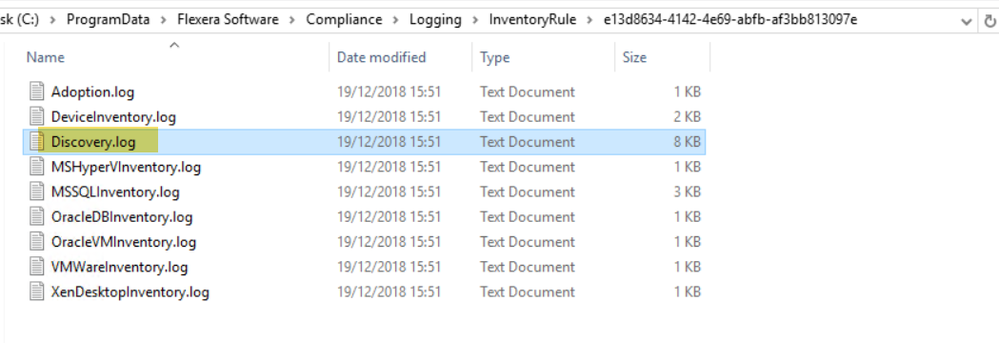
Open up the discovery.log in a notepad viewer
You should now see the IP argument targeting your chosen network card as we entered in the registry
It is worth noting that MGSIPSCAN.exe is a Flexera Branded version of Nmap- https://nmap.org/
so in theory, while I have not tested this you could feed it other Nmap arguments although your mileage may vary as this is unsupported by the flexera product
That said, here is a useful list of commands that could come in handy for this:
Jun 30, 2020 09:38 AM
-
Cloud
-
FlexNet Manager Suite 2014
-
FlexNet Manager Suite 2014 R2
-
FlexNet Manager Suite 2014 R3
-
FlexNet Manager Suite 2015
-
FlexNet Manager Suite 2015 R2
-
FlexNet Manager Suite 2015 R2 SP1
-
FlexNet Manager Suite 2015 R2 SP2
-
FlexNet Manager Suite 2015 R2 SP3
-
FlexNet Manager Suite 2015 R2 SP4
-
FlexNet Manager Suite 2015 R2 SP5
-
FlexNet Manager Suite 2016
-
FlexNet Manager Suite 2016 R1 SP1
-
FlexNet Manager Suite 2017 R1
-
FlexNet Manager Suite 2017 R2
-
FlexNet Manager Suite 2017 R3
-
FlexNet Manager Suite 2018 R1
-
FlexNet Manager Suite 2018 R2
-
FlexNet Manager Suite 2019 R1
-
FlexNet Manager Suite 2019 R2
-
How to
-
On-premises
-
VMware