- Flexera Community
- :
- Software Vulnerability Management
- :
- Software Vulnerability Management Blog
- :
- Third Party Thursday: A total vulnerability May-hem
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Third Party Thursday provides a helicopter view over the software vulnerabilities reported by Secunia Research at Flexera each month. We aim to help you identify which software products and vendors did introduce new security risk. This blog looks to answer important questions which often surface in the mind of vulnerability managers and security administrators. You can review my first blog for more examples on how I do this.
Today, let's dive into exploring the following questions:
• Which are the most critical and widespread vulnerabilities between April 26 and May 23?
• Why one should not blindly trust public vulnerability information that lacks research analysis depth?
• What vulnerability factors contribute for more accurate and in-depth research analysis?
• How does Flexera SVR help you immediately track new vulnerabilities affecting your software assets?
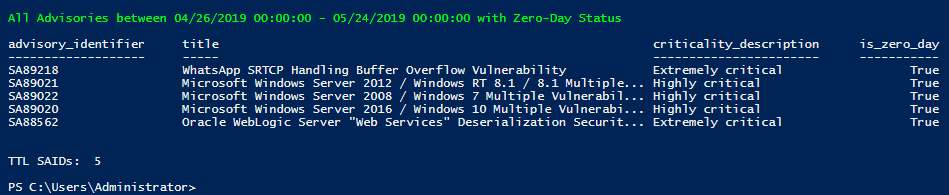
Secunia Research released 406 new Secunia Advisory IDs in this period. Five of those have received zero-day status, which is far more than usual for one month. In 2017, Flexera reported 14 zero-day exploits over the course of 12 months and 16 zero-day SAIDs for all of 2018.
Having five big zero days in a span of one month means a lot of exploits are happening in the wild, especially considering the worst vulnerability during that month is not even a zero-day.
Vulnerabilities in nearly 55% of all new advisories have a known exploit, according to Flexera Threat Intelligence data. A staggering 13% of all security advisories reported on security issues that reside in the Very Critical threat score range, mostly because of the introduction of ZombieLoad, RIDL, Fallout.
More than 50% of all issued advisories in this period reported remotely exploitable software vulnerabilities.
Fifty-nine advisories have been assigned Highly Critical or Extremely Critical ratings. This is a more than 5% drop in the number of advisories with high severity rating, compared to the 17.3% reported in April.
A smaller number of advisories with high severity ratings does not necessarily represent smaller risk. Targeted attacks for example frequently utilize seemingly moderate or less critical vulnerabilities to gain further access to an infrastructure.
There have been a number of high-profile vulnerabilities disclosed in a matter of 5 days which can severely affect millions of private and corporate devices. The number of zero-day vulnerabilities is indicative of the increasing risk of exploitation, which is also confirmed by the EU data protection authorities. The EU announced nearly 90.000 breach notifications under GDPR since it was adopted approximately one year ago. This statistic averages out to 246 successful security breaches per day.
BlueKeep = Ghosts from the Past
Microsoft introduced to the world a new ‘wormable’ Zero-Day flaw reported through SA89022 and identified in CVE-2019-0708. The news came exactly two years after the WannaCry cyberattack. It brought ghosts from the recent past, as the current flaw is similar to the issues exploited back then.
A week before the publication of CVE-2019-0708, Baltimore’s city government had already been dealing with what seems to be an EternalBlue cyberattack exploit that was previously used for WannaCry. While this exploit is still haunting us, it is said to also be able to exploit the new RDS issue, dubbed BlueKeep, which represents immediate danger for the nearly one million affected systems across the world.
Microsoft published patches for supported and unsupported versions of Windows to protect all customers from the widespread impact, as the issue may also have impact on ICSs and Healthcare environments. While Microsoft offers these patches, it needs to be stressed that products should never be used beyond their supported product life-cycle. Customers should upgrade to a secure supported product version.
WhatsApp Pegasus?
While the situation with Microsoft was unfolding, a number of accredited public sources reported that targeted cyber-attacks are happening in the wild where hackers where able to install the infamous spying software Pegasus on the phone of a human rights lawyer who is actively working on a case against the same group NSO that originally developed Pegasus. The unknown hackers used a buffer overflow vulnerability in WhatsApp VOIP stack identified in CVE-2019-3568. In just a few days, we saw yet another repeating use case of famous exploit code that is causing havoc again.
WhatsApp has been reported by Flexera as a zero day in advisory SA89218. Facebook published a patch with the vulnerability becoming public, but it is likely that many users would have problems immediately updating their application versions. And there is likely someone, somewhere cracking it already.
The existence of a security patch makes this issue somewhat controllable, as is the case for BlueKeep. Everyone should patch their devices exposed to these vulnerabilities because both have very high severity and require as little human interaction as possible to be successfully exploited. This is not necessarily the case with the new Intel side-channel attacks that were also disclosed at about the same time as the other two.
Intel >= Doomsday
Just when we thought we have seen how bad things can be, Intel escalated the situation “carefully” with a coordinated public disclosure of new Spectre-like side-channel attacks named ZombieLoad, RIDL, and Fallout.
One problem of the Speculative execution processing optimization technique in Intel chips is that the memory access isn’t properly checked for authorization before being executed thereby allowing access to e.g. restricted memory areas. These hardware-based security weaknesses are present on all Intel chips produced since 2011.
The impact is so widespread that you are likely to find a vulnerable system at every:
- computer with a recent Intel Processor [thus including every modern macOS system]
- small business office [that has PC with Intel processor]
- corporate network and every datacenter [the issues affect both on-prem and Cloud]
- every corner of the world where Intel sold modern processor chips for the past 7-8 years
The main problem with these vulnerabilities is that they are hardware based and very hard to fix. It boils down to how these chips are designed and what their inner workings are. Speculative Execution vulnerabilities are deeply embedded in the hardware.
It is very difficult, if not impossible, to completely solve them without replacing the hardware chips that contain the vulnerabilities. Intel seems to be losing a lot of friends since this vulnerability disclosure is a history-repeating for them after Spectre and Meltdown.
What vendors exposed to these vulnerabilities can do is try to solve the problem by introducing software counter-measures against a hardware-based vulnerability. Such mitigation techniques typically mean slowing down the processing speeds and limiting the overall system performances.
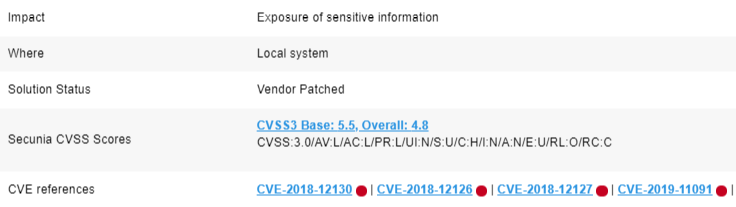
ZombieLoad, RIDL and Fallout issues identified by 2018-12130, CVE-2018-12126, CVE-2018-12127, CVE-2019-11091 may get exploited through a variety of products like VM hypervisors and all major operating systems. The impact of these issues is extremely widespread and the expected impact is essentially information disclosure.
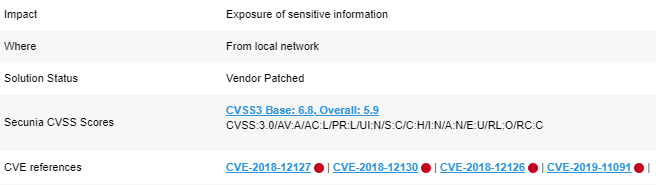
The recent vulnerabilities reported by Intel allow, in the worst-case, an unprivileged virtual machine guest user to access core system information about the physical host and privileged-user-only information the system is processing. This may also include sensitive data belonging to other cloud-provided customers that shall otherwise be fully restricted for access by anyone else but the very customer paying for Cloud privacy.
However, product context is also one of the corner stones of an analysis as mentioned before. On an operating system without virtualization at play, a local unprivileged user would be required to gain access to restricted information.
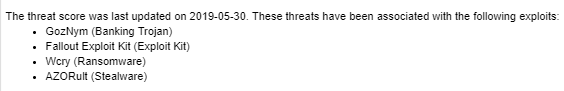
Flexera Threat Intelligence data tells us that there are a number of exploit codes that can actively be used to target the vulnerabilities and exploit them. This means businesses literally have no time for planning the remediation. Every second of the clock ticking away increases the likelihood of an eventual exploitation happening.
Businesses have several problems to deal with:
- Visibility – Identification of each separate software exposed to ZombieLoad, RIDL and Fallout is required. You also need Threat Intelligence data to be aware of which issues already have evidence of exploitation (as per my example above).
- Research depth and accuracy – In-depth intelligence on the correct attack vectors and severity for each software being impacted is required for orderly and timely prioritization. This certainly includes consideration of the product and user contexts and best-security practices when the final scoring analysis is being made to ensure that the intelligence is not misleading you.
- Continuous monitoring – All software assets must be tracked continuously for reports arriving lately by some vendors, and for additional advisory updates of the originally issued SAIDs.
The Software Vulnerability Research solution empowered by Secunia Research intelligence can guarantee immediate reporting on these vulnerabilities (and any other mentioned in this blog) through correct risk identification and focus on the product and local user contexts which are extremely important for correct research analysis. Flexera has issued 52 independent SAIDs between April 26 and May 23 for the Intel-related vulnerabilities thus far identifying each software product impacted.
Opposed to other public vulnerability reporters who tend to do simple risk metrics calculations to come up with their criticality and CVSS scores, Secunia Research digs much deeper into its analysis. The team takes under consideration the “User Context,” “Product Context,” best-security practices and other important risk factors that help identify the true risk by, and the true gains for, a hacker. Flexera is often required to reject vulnerability information from other reporters that lack research depth, which should tell you how much noise there is mixed with the real threats.
Having a research team that does all the verification and fact-checking for you and provides you with deepest possible vulnerability analysis is essential for the overall long-term success of every security remediation program. Besides depth and accuracy of the research, you should also be able to trust a very wide coverage of products and versions that fall under the scope of this reliable research analysis, to ensure that all of your applications are supported by your intelligence vendor, and you don’t miss out on important risks that require prioritization. This should also cover EOL software since it is often easier to forget/ignore EOL programs with hundreds of severe vulnerabilities disclosed on a monthly basis.
What about the rest?
Oh, it has certainly not been easy for me to provide you with a short blog post. I would understand if you already had enough reading and you just want to go do something that is more fun. But would you? Given the fact that we have so far covered several flaws which have been linked to nearly 60 SAIDs (RDS/WhatsApp/Intel), we still have a whole plethora of risky insecure applications to cover.
The “Enterprise” Ones
Oracle had one zero-day advisory reported on April 26 by Flexera and 22 other SAIDs reporting on security issues with Oracle Linux and Solaris. The zero day must be prioritized immediately for obvious reasons. SA88562 is linked to very critical threat score and was identified with Extremely Critical rating:
“Vulnerability in the Oracle WebLogic Server component of Oracle Fusion Middleware (subcomponent: Web Services). Easily exploitable vulnerability allows unauthenticated attacker with network access via HTTP to compromise Oracle WebLogic Server. Successful attacks of this vulnerability can result in takeover of Oracle WebLogic Server.”
Microsoft claimed two other zero-day advisories, namely SA89021 and SA89020, referring to a number of issues in Windows 8.1/2012 and Windows 10/2016 versions respectively. A total of 21 SAIDs are been attributed to Microsoft for their zero days and all other issues reported during Patch Tuesday (May 9).
As usual, IBM is responsible for a plethora of vulnerability advisories. Flexera issued 74 SAIDs for IBM, while in April there were 63 other.
Another prominent monthly player is Cisco. They have large hardware and software manufacturing portfolios and their de-facto standards result in high vulnerability volumes. Just like IBM, they are subject to a lot of vulnerability research. Cisco was linked to 36 new Secunia Advisory IDs.
Lenovo, Hitachi, VMWare, Samba, Citrix, Micro Focus, HUAWEI and SAP have also had some of their products listed as vulnerable in a total of nineteen security advisories between April 26 and May 23.
The “Common” Ones
Secunia published three new SAIDs for Mozilla Firefox 66.x, ESR and Mozilla Thunderbird. Each advisory sums up multiple vulnerabilities. For instance, SA89029 for Firefox reports on 14 security flaws alone. You should patch Firefox 67.x and additionally check the vendor website for more information.
In this period, multiple vulnerabilities have been reported in Google Chrome through SA88628 and SA89047. Adobe also published new security patches for a vulnerability in Adobe Flash and multiple issues in Adobe Reader/Acrobat as reported through SA88905 and SA88918 by Flexera.
Besides the Secunia Advisory ID for macOS which concerns the speculative execution issues we talked about earlier, Apple also had to patch multiple vulnerabilities in their TV, iOS, and Safari browser products as reflected by Flexera in SA88960, SA88791, SA88953, SA88921.
All of the commonly used software had Highly Critical ratings and Low-Medium threat scores. All common applications require quick patch prioritization across the domain due to their global popularity and impact. You should also patch newly vulnerable Wireshark, Waterfox, Tableau and Npcap.
The “Secure” Ones
This list is always my favorite because it kind of goes to show where investments should be made in better code security before granting the right to others to maintain theirs on their behalf. Here is the list of security vendors that had security vulnerabilities reported by Flexera as well as other public sources:
F5; Checkpoint; RSA Security; CyberArk; Sophos; Symantec
The “Web & Email” Ones
Open X-Change and NetApp vulnerabilities were reported in two security advisories each, while Dovecot, Drupal and Joomla had one each. Apache and Atlassian had lead count of six security advisories each.
The “Dev & Unix” Ones
In the development area, you should look to patch quickly your GitLab, Jenkins, PHP, Python, GO, Eclipse, FasterXML Jackson servers and applications and also the Linux flavors you are maintaining:
- Ubuntu = 32 SAIDs
- SUSE = 24 SAIDs
- Debian = 12 SAIDs
- Red Hat = 28 SAIDs
- Amazon Linux = 15 SAIDs
- Alpine Linux = 2 SAIDs
- Oracle Linux = 20 SAIDs
- Oracle Solaris = 1 SAID
- CentOS = 9 SAIDs
You should consider that 82% of all 52 SAIDs linked to ZombieLoad, RIDL, and Fallout vulnerabilities have been issued for Unix-based systems and services. Full list of the SAIDs is available through Flexera SVR.
The “Other” Ones
Here I outlined the remaining vendors which have vulnerabilities attributed to their name over the period I cover here. These vendors had one or a few advisories during the month that need handling.
Linux Kernel [SAIDs linked to ZombieLoad], XEN, Poppler, Freeimage, phpBB, phpKF, QEMU, cURL, Boostnote, systemd, Moodle, Common Desktop Environment, FreeBSD, LibreOffice, NSClient, Azul Zulu, memcached, OTRS, Jetty, eXtplorer, QlikView, TIBCO, MariaDB, Slack, Intel Graphics, NVIDIA, Xerox, Lexmark, QNAP, Origin, Polycom, Schneider Electric, Siemens.
Conclusions
Let me finish by saying that any vulnerability reported by Secunia Research should be expected to shortly result in exploits / PoCs (Proof of Concepts). Zero-Day status assigned by Secunia Research to any advisory ID should be perceived with maximum urgency and resolved immediately by the business.
The likelihood of reverse engineering a vulnerability and creating PoC shortly after is considered a highly likely probability by Flexera. Secunia Research analyzes vulnerability risk with a maximum research depth. Flexera applies its own proprietary Secunia Research vulnerability ratings to each vulnerability based on the resulting analysis that takes under consideration a lot of additional exploitation factors and in turn allows our customers to truly prioritize vulnerabilities through this normalization – regardless of source of vulnerability information.
This helps Flexera identify more accurately than others if a vulnerability can only be exploited after violation of best-security practices, or the vulnerability is exploitable without such violations.
For example, if an only directly exploitable vulnerability exists in the management interface of your firewall, you would not want to have this interface open to the Wide Area Network because this will be a violation of best-security practices. Thus, a fully Remote Attack vector for this vulnerability is unrealistic since exploitation could occur from the “Adjacent Network” only (from within a corporate network, typically management network) where all users are authenticated and therefore the overall criticality and CVSS ratings would be corrected by Flexera accordingly to represent the real threat factor and vectors, opposed to many other reporters who will fail to recognize the additional factors such as the User and Product usage contexts and best-practices violations. This is one example of how Secunia Research can help you identify risk accurately.
When you find yourself in a situation to be looking at hundreds of vulnerabilities that need equal attention and you don’t know where to start, Threat Intelligence helps you figure it out with a single look into the insights it provides. By looking at Threat Intelligence scores, you will often find yourself having a clear idea where to begin patching and which issues are being targeted.
During such a month with so many high profile issues, prioritizing the high-visibility ones while leaving the rest untouched would be unwise. With Flexera SVR’s comprehensive product and vendor database coverage in terms of vulnerability tracking, you can cut effectively through the noise and recognize vulnerabilities and the vulnerable products instantly with no delays. This should help you act quickly and efficiently to close the risk window before anyone has a chance to profile your networks.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
- New and Improved Threat Scores in SVM and SVR in Software Vulnerability Management Blog
- Monthly Vulnerability Review: September 2019 in Software Vulnerability Management Blog
- Third Party Thursday: Harness the power of Vulnerability Intelligence in Software Vulnerability Management Blog
- Third Party Thursday: Focus on what matters and patch in Software Vulnerability Management Blog
- Third Party Thursday: monthly vulnerability trends in Software Vulnerability Management Blog