- Flexera Community
- :
- Software Vulnerability Management
- :
- Software Vulnerability Management Release Blog
- :
- SVM December Update for Log4j Detection
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Being aware of vulnerable software in your environment and being able to patch them to be on a secure version has become extremely critical after the exposure of the recent Apache’s Log4j vulnerability. We understand this importance and have been on top of this global issue right from the moment of its disclosure to design a solution in SVM to help you with the awareness of the presence of this extremely critical vulnerability in their environment. Today’s release of SVM adds enhancement to the host agent and the scanning logic to detect log4j files.
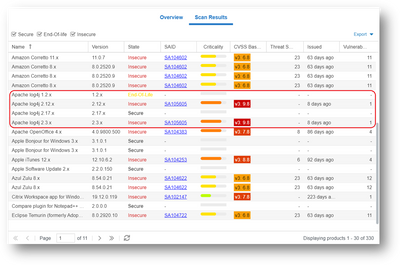
The SVM's Single Host Agent (v7.6.0.19) can now detect the log4j jar files installed on a host machine. The scan type must be set to either 2 or 3 for the agent to detect log4j jar files. SVM will identify the version of the detected log4j file and categorize it as Secure, Insecure and EOL, to make you aware of vulnerable log4j versions in your environment. It is important to note that only the log4j-core*.jar files are found to be vulnerable, therefore SVM detects only these files during the scan.
The log4j component may have been installed as a part of any software on a machine, however, when it is detected, SVM will associate it with the product Apache Log4j in the Scan Result view for a host. There will be a need to manually review the path of the log4j file in the scan results to identify the actual product which installed this file on the host. You must follow up with the vendor of the product to either get a patched version or follow the recommendation from the vendor to fix this vulnerable file in the product.
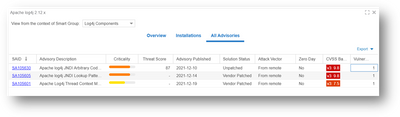
Secunia Advisories are authored for these vulnerabilities to give you insights about this vulnerability with details on impacted versions of log4j.
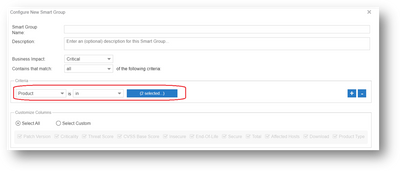
You may take advantage of Smart Groups to configure a new smart group to get a list of all the log4j versions installed across various hosts in your environment, to help you prioritize and focus on these products/hosts immediately. Under the Product Smart Groups, use the criteria as shown in the below screenshots to get the list of log4j versions in your environment:
Smart Group results:
At this point, our goal was to give a quick solution to help you detect log4j vulnerable files in your environment for your immediate attention. We will continue monitoring updates on this vulnerability and add enhancements to this solution as and when applicable.
For the status of impacted Flexera products, please see this announcement.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
- SVM On-prem December 2023 Update in Software Vulnerability Management Release Blog
- SVR December 2023 Update in Software Vulnerability Management Release Blog
- SVM December 2023 Update in Software Vulnerability Management Release Blog
- Firefox ESR 115.3 64-bit SPS Package in Software Vulnerability Management Forum
- Monthly Vulnerability Insights: December 2022 in Software Vulnerability Management Blog