- Flexera Community
- :
- Flexera One
- :
- Flexera One Knowledge Base
- :
- Troubleshooting Policy Errors
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Flexera's policy management solution allows IT teams to apply policies to their organization's IT assets, ensuring compliance with security standards and regulatory requirements. However, sometimes errors may occur when policies are applied. One common cause of policy application errors are insufficient user permissions.
In this article, we will cover how to troubleshoot policy application errors by checking that the required permissions are set for the user that is applying the policy.
Troubleshooting Steps:
- Check the User's Permissions: The first step to troubleshooting policy application errors is to verify that the user who is attempting to apply the policy has the necessary permissions. Check that the user has the correct permissions to access the policy and apply it to the target asset.
- Check the Asset's Permissions: In addition to checking the user's permissions, you should also check the target asset's permissions. Verify that the user has the correct permissions to access and modify the asset. You can check the asset's permissions by reviewing its access control settings.
- Check the Policy Settings: Next, review the policy settings to ensure that they are configured correctly. Verify that the policy's conditions and actions are configured correctly and that they match the requirements of the target asset.
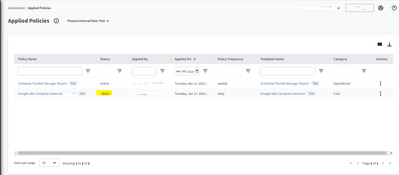
- Check the Policy Status: Check the status of the policy to determine if there are any issues with its deployment or activation. Ensure that the policy is enabled and active.
- Check the Logs: Finally, check the logs to identify any errors or issues that occurred during the policy application process. The logs can provide valuable information to help you diagnose and resolve policy application errors.
Conclusion
Policy application errors can be frustrating and time-consuming to troubleshoot. However, by following the steps outlined in this article, you can quickly identify and resolve issues related to user permissions. Remember to check the user's permissions, asset's permissions, policy settings, policy status, and logs to determine the root cause of the error. By doing so, you can ensure that policies are applied successfully and that your organization remains compliant with security standards and regulatory requirements.
Aug 07, 2023 01:37 PM