- Flexera Community
- :
- Software Vulnerability Management
- :
- Software Vulnerability Manager Knowledge Base
- :
- Why are SPS patches auto-Approved in WSUS?
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Summary
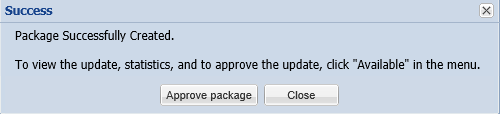
You published a new SPS patch through the Software Vulnerability Manager to a Windows Server Update Services server (WSUS), but even when you have clicked to "Approve" the update through the incoming options window, your patches are still being deployed to more systems than what you've approved.
Symptoms
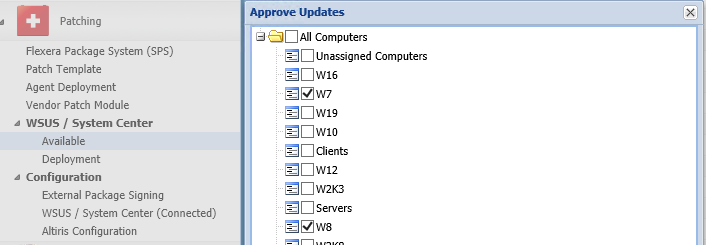
You may have noticed that the Software Vulnerability Manager package is actually set to approve before you did it yourself. This blocks you from executing the planned package distribution because even when you set an approval, it doesn't seem to work or take the expected effect. For example, when you decide to not approve a patch immediately but to do it from the "Available" section under the Patching menu.
Cause
There are a few things to understand here.
- SVM Packages are classified as Security/Critical Update after published to a WSUS (+SCCM) server.
- WSUS (SCCM's SUP ) has been configured to auto-approve Security/Critical updates to all hosts.
- Once any package is approved at WSUS, you cannot override the first with a direct second.
This may happen without you realizing how this happened and when because it is pretty common auto-approvals to be set for e.g. Windows Defender security definition updates.
The Software Vulnerability Manager surrenders the package to the WSUS server after publishing and you 'll have to tweak your WSUS to adjust its configuration to be working for you. Or, you may not have to.
Resolution
You can take one of three options:
- Disable the Automatic approval rule from your WSUS if that is not going to prevent your other security patch management programs. This will allow you granular deployment control.
- Keep the Automatic approval rule and decline the updates at the "Available" menu of the web interface of the Software Vulnerability Manager, as soon as you publish them.
- Modify the existing rule to apply only to specific Microsoft products.
on
Nov 15, 2018
05:29 PM
- edited on
Sep 27, 2019
03:21 PM
by
![]() RDanailov
RDanailov