- Flexera Community
- :
- Software Vulnerability Management
- :
- Software Vulnerability Manager Knowledge Base
- :
- Enable SVM-to-WSUS SSL publishing via IIS 8.5
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Summary
In this article, you will learn to configure SSL at WSUS and integrate SVM with it for secure publishing.
This provides all the steps, but it should act as an example.
You should always implement your services through the most current encryption and security standard.
Discussion
The following will take you through all steps.
Requirements
- You installed Windows Server Update Services (WSUS) role on a Windows Server machine
- You have surpassed the initial configuration of the server in terms of products and classifications.
- Your Windows account is added to the WSUS-local security group "WSUS Administrators".
NOTE: This article provides examples for Windows Server 2012 R2 installation of WSUS, but you will likely be able to apply the same, or similar steps for higher versions of Windows Server Update Services.
Configure SSL at Microsoft Internet Information Services 8.5
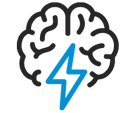
1) Open the Server Manager, navigate to Tools > Internet Information Services (IIS) Manager.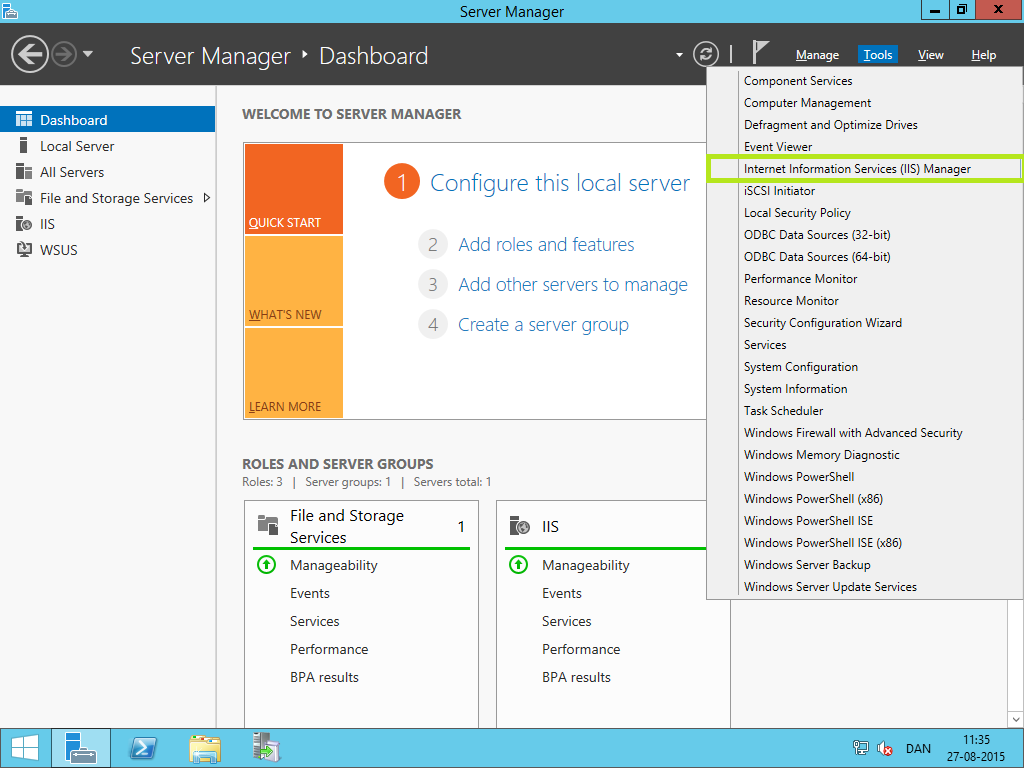
2) Click the server node in the tree. Double-click on "Server Certificates".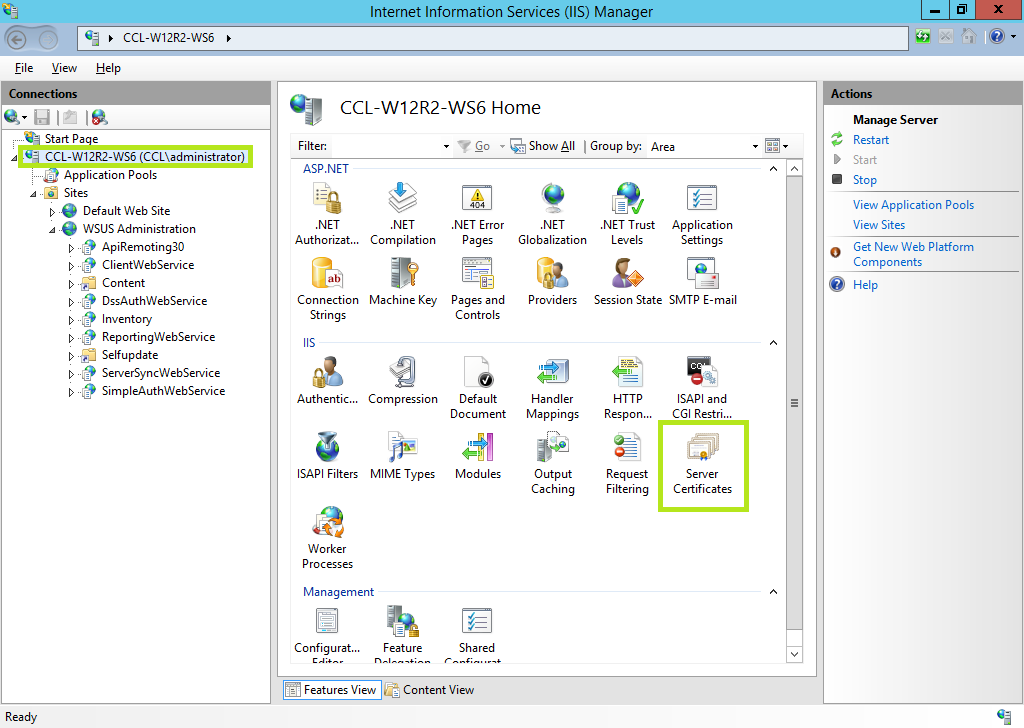
3) Here you have two options.
- Use your own CA SSL certificate (highly suggested):
- Choose "Import",
- Proceed with step 4.a.
- Create a self-signed SSL certificate
- choose "Create Self-Signed Certificate.":
- Go with step 4b.
4a) Select your CA SSL certificate [PFX format], provide the password and choose "Web hosting". 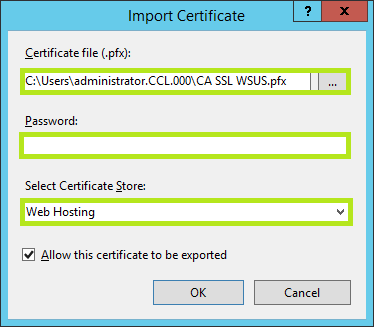
4b) Provide a friendly name for the certificate. Choose. "Web Hosting" store and close it with OK.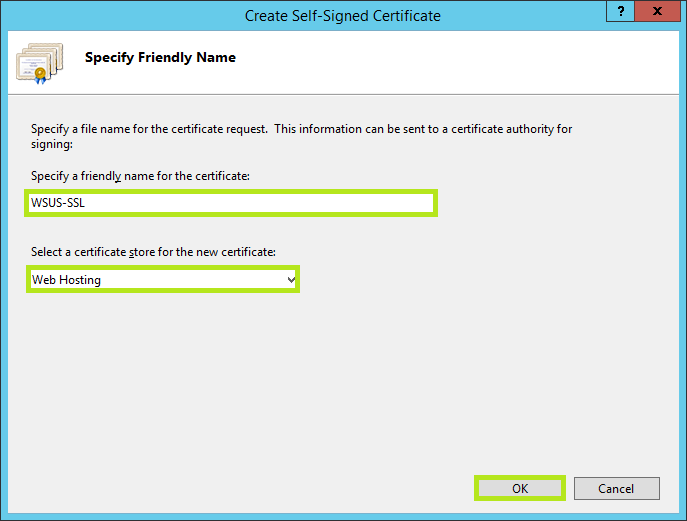
5) Choose "WSUS Administration" in the left-hand sided tree list.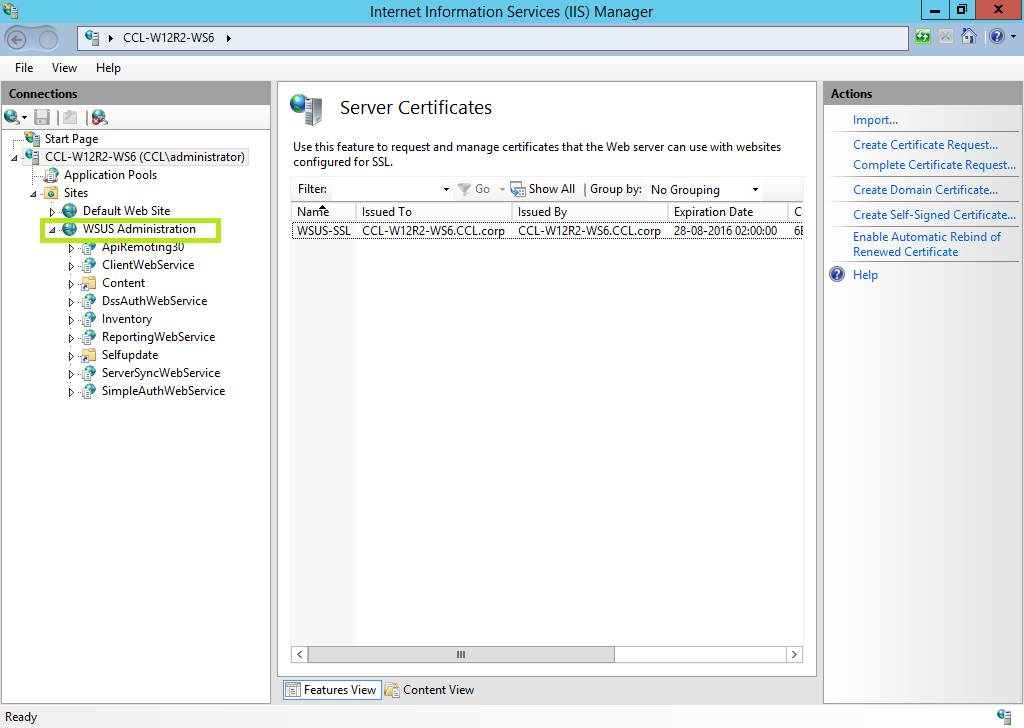
6) Choose "Bindings" in the Actions column.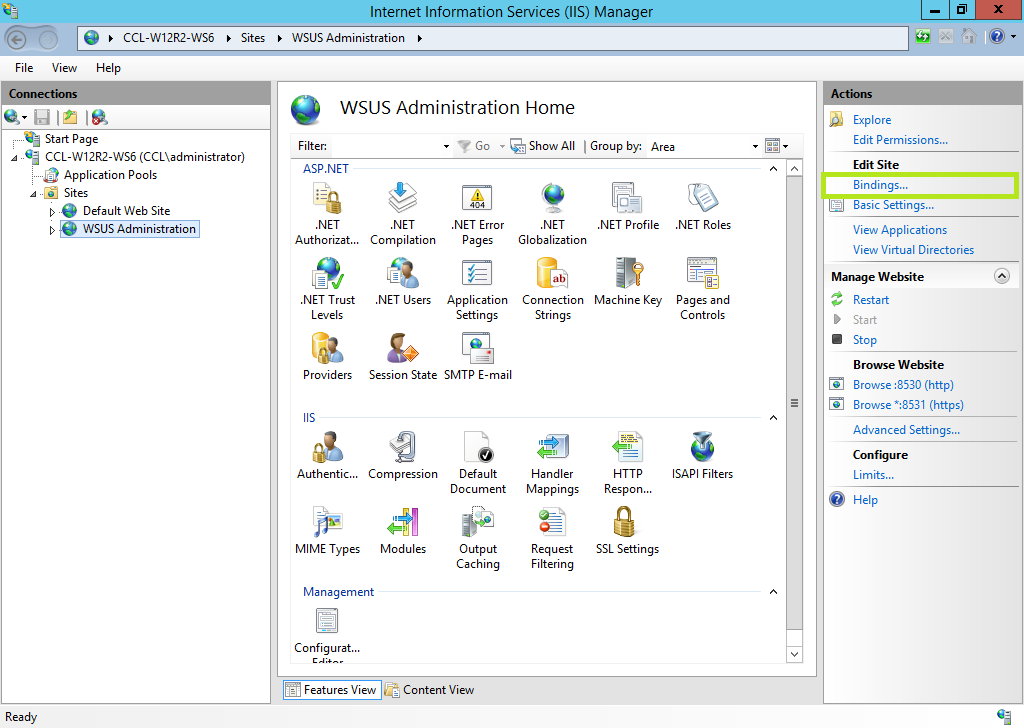
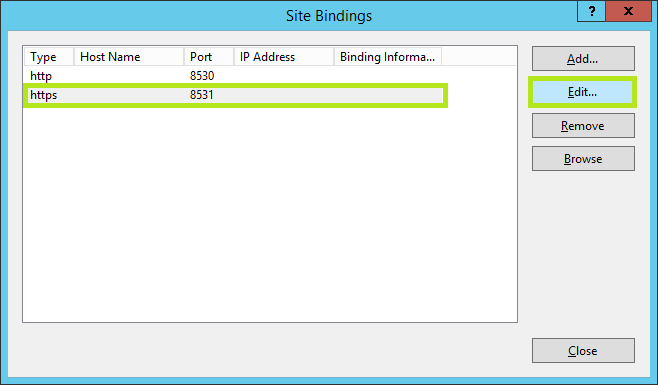
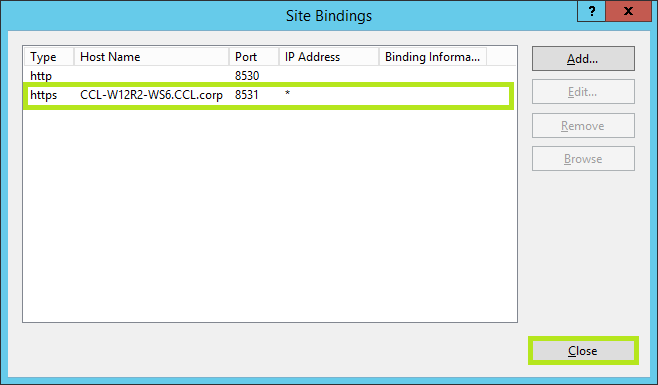
7) Click on "https 8531" and choose "Edit"
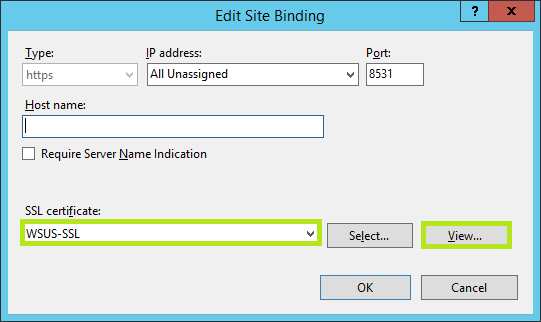
😎 Select the SSL certificate in the drop-down box and click "View...".
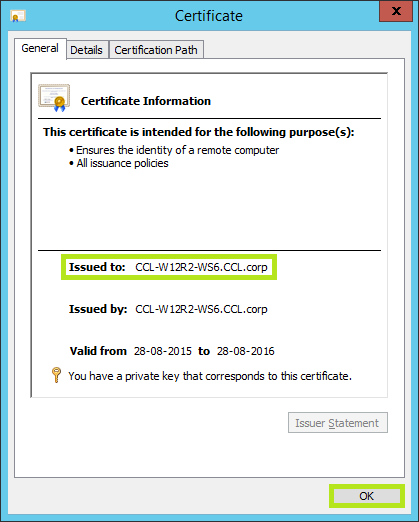
9) Make a note of the FQDN of the "Issued to" server and click OK.
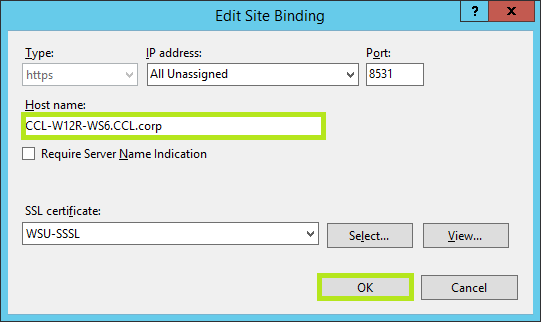
10) Provide the FQDN hostname from the previous step and click OK.
11) Click Close.
12.) Click on WSUS Administration Console, select SSL Settings, then enable 'Require SSL' next.
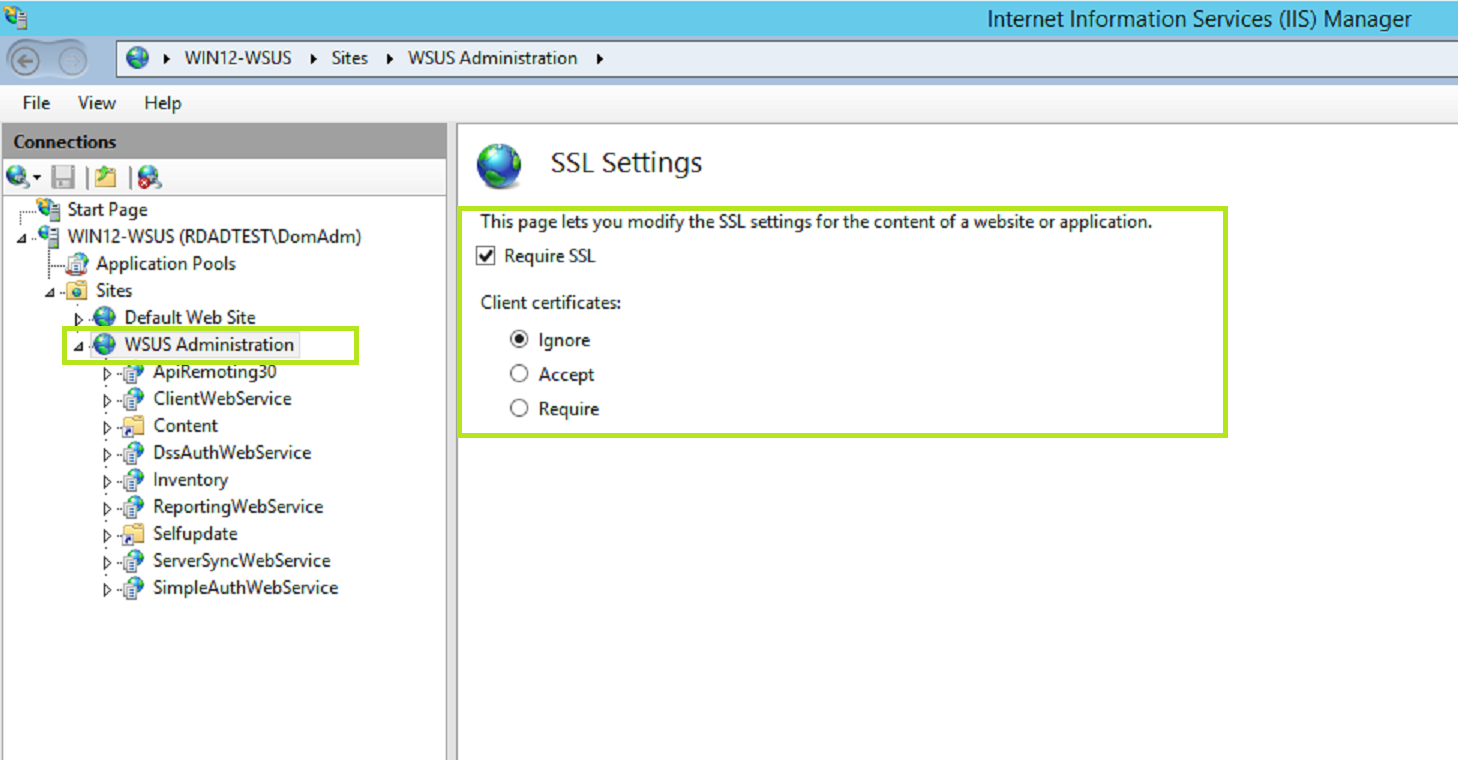
12) Expand "WSUS Administration" . Choose "ClientWebService". Double-click "SSL Settings".
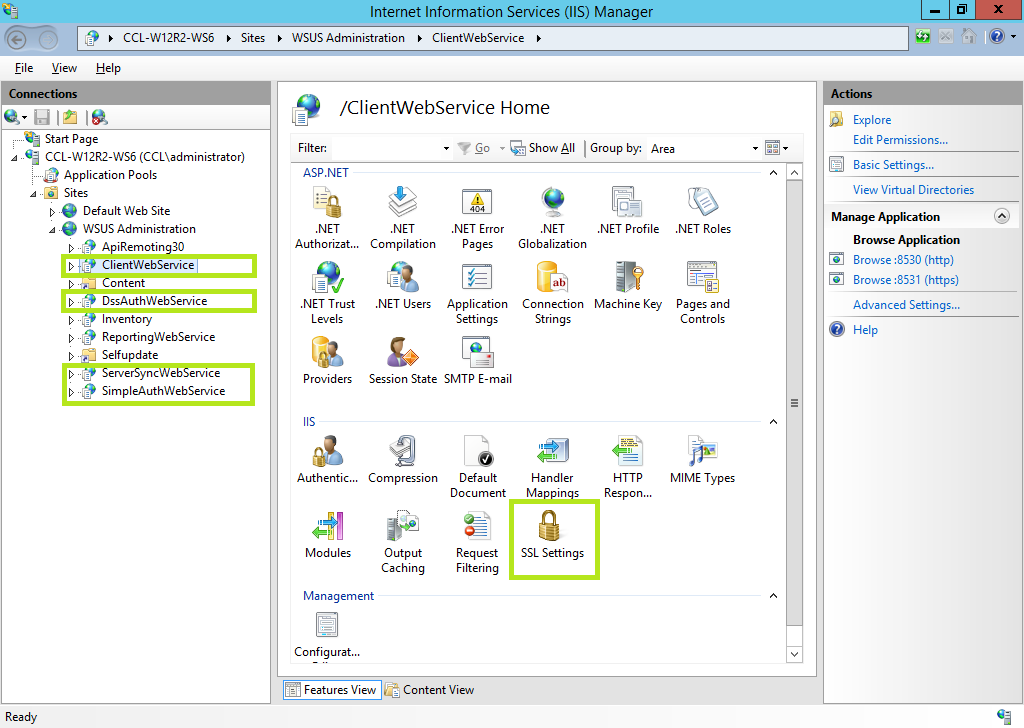
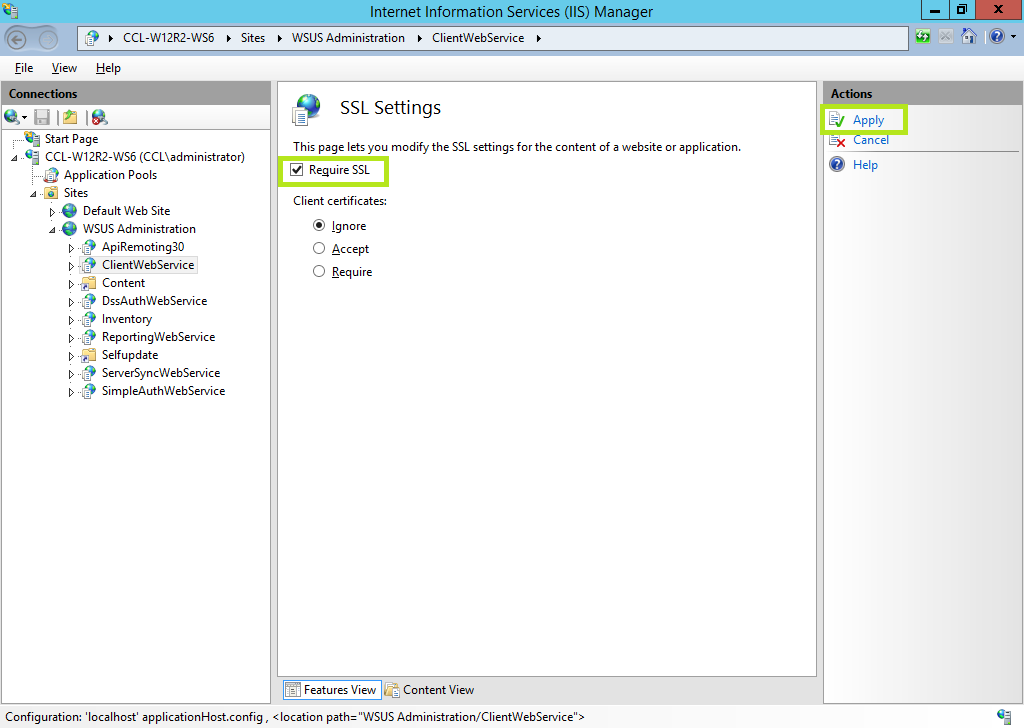
13) Mark the checkbox "Require SSL" . Click Apply.
14) Repeat steps 12 and 13 for "DssAuthWebService", "ServerSyncWebService", and "SimpleAuthWebService". Close the "Internet Information Services (IIS) Manager".
Validate changes with WsusUtil.exe
15) Run command prompt in Administrator mode.
16) Change to directory C:\Program Files\Update Services\Tools.
17) Run "WsusUtil.exe configuressl <FQDN>". The output should be similar as shown below. 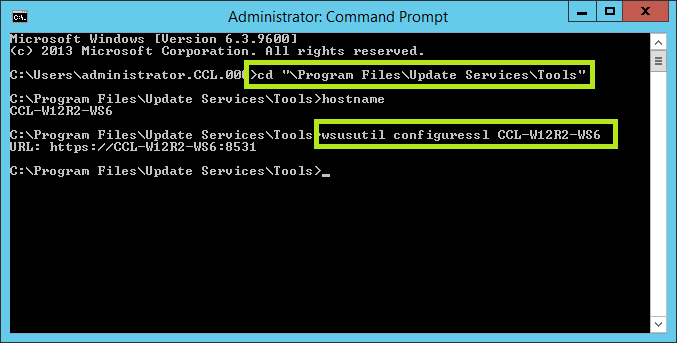
Export and Distribute SSL Certificate
The next step is to export this certificate and provide it to all systems connecting to WSUS.
18) Run MMC as admin. Click File and choose "Add/Remove Snap-in"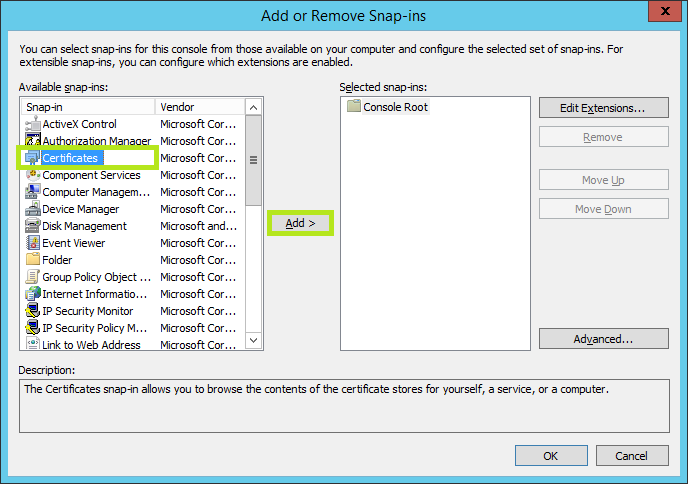
19) Click Certificates and then click Add.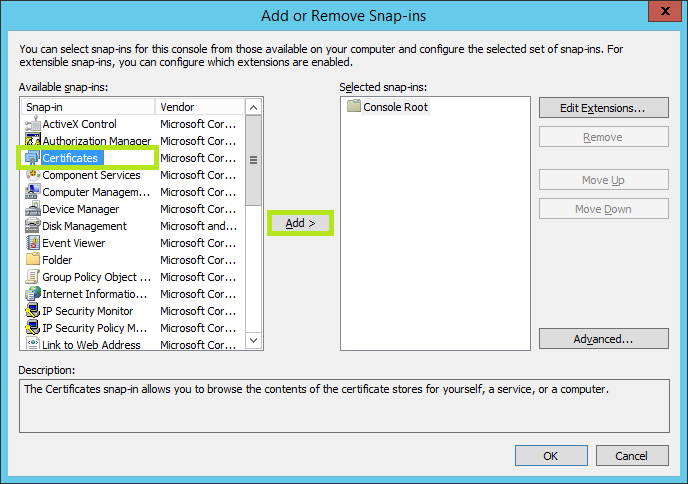
20) Enable "Computer account" and click Next.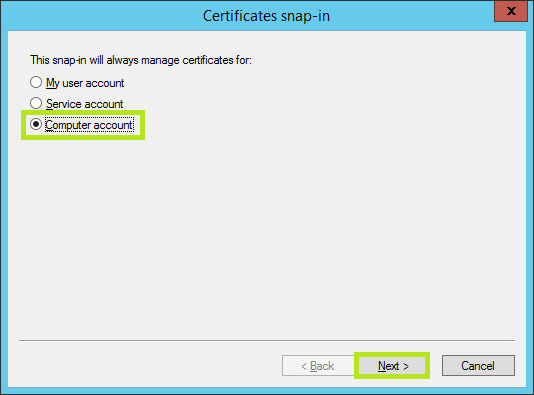
21) Choose "Local computer" and click Finish. Click OK after that. 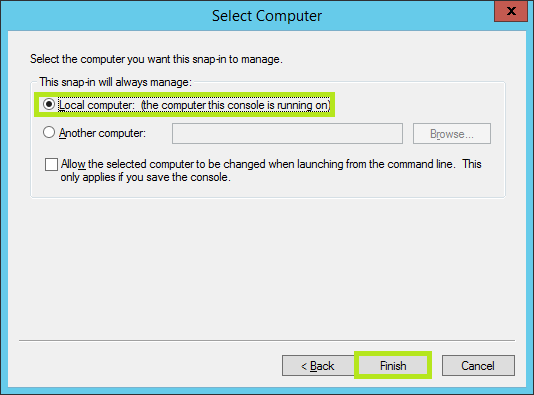
22) Expand the Certificates (Local Computer) \ Trusted Root Certification Authorities.
23) Click on Certificates. Locate the certificate that matches the FQDN of this server.
24) Right-click and choose "All Tasks" and "Export"
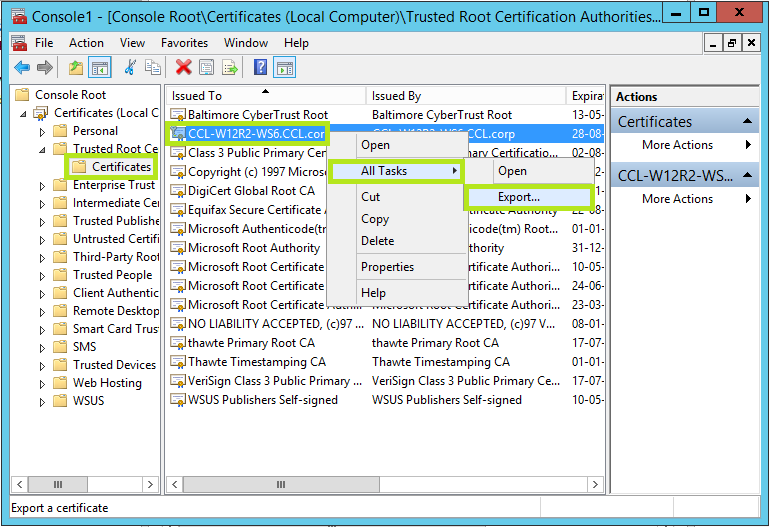
Now the certificate has been exported, you will need to provide this certificate to all systems that will need to connect to the WSUS server (SCCM, WU agents, SCCM clients).
This certificate should be imported to the "Trusted Root Certification Authorities" (This can also be achieved by creating a GPO). WSUS should be configured to use SSL and you should be able to integrate the Software Vulnerability Manager interface with the WSUS server using SSL.
Connect SVM to WSUS via SSL
25) In the Patching menu, navigate to Patching, choose Configuration -> WSUS/System Center.
26) Provide the FQDN as the WSUS server name (as in step 9).
27) Enter the correct WSUS SSL port, enable "Use SSL Connection" checkbox, then press Connect.
28) Verify the connection in the connection status.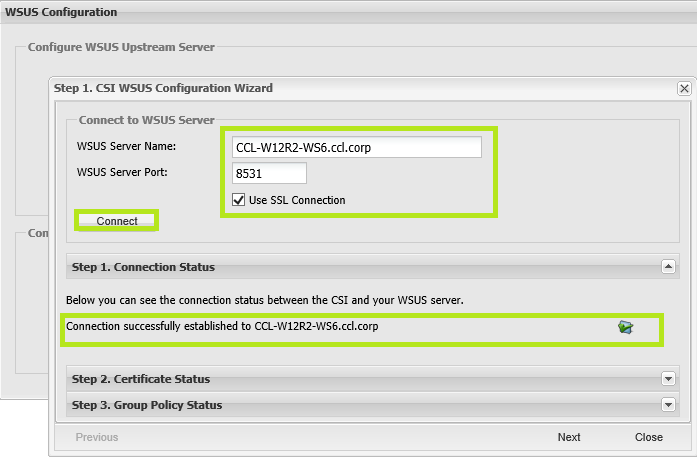
on
Jul 17, 2018
10:51 AM
- edited on
Sep 19, 2019
04:27 PM
by
![]() RDanailov
RDanailov
