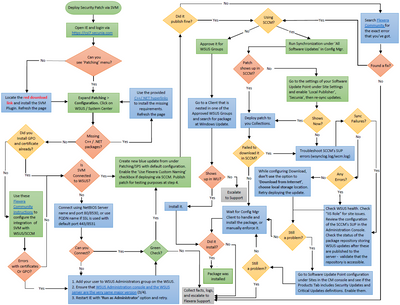
Integrate SVM with WSUS/SCCM and Deploy a Patch [Logic Flow Map]
Users often require additional help for the logical process workflow when it comes to integrating the Software Vulnerability Manager 2019 software to their internal WSUS or SCCM servers for patching. In most, users need additional elaboration on wha...