- Flexera Community
- :
- Software Vulnerability Management
- :
- Software Vulnerability Manager Knowledge Base
- :
- Create the WSUS-CSI Group Policy Manually
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Summary
A full guide on how to create a GPO to distribute WSUS certificate and Windows update settings.
Synopsis
This short guide describes how to create a Group Policy Object (GPO) for CSI-WSUS by using the Group Policy Management console. Once the GPO is created and linked to the correct Organizational Unit (OUs), the computers in that OU will download the WSUS publisher's self-signed certificate and Windows settings so that third-party updates can be downloaded correctly.
Discussion
Login to your Software Vulnerability Manager account.
Navigate to Patching > Configuration > WSUS / System Center > Configure Upstream Server.
Connect to the WSUS server and then click Next.
On Step 2, click "Export Signing Certificate" which will be saved to your documents folder.
 Example of exporting the certificate
Example of exporting the certificate- Launch the Group Policy Management Console on your Domain Controller.
- Navigate to Group Policy Management > Forest > Domains > Organizational Unit
- Right-click the Organizational Unit > Create a GPO in this domain, and Link it here > Name the GPO e.g. ''CSI-WSUS' or as per your policy.
- Right-click the GPO and click Edit
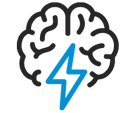
- Navigate to Computer Configuration > Policies > Windows Settings > Security Settings > Public Key Policies
- Import the previously exported "wsuskey.cer" Certificate in the ''Trusted Root Certification Authorities'' and ''Trusted Publishers'' Folders
- Navigate to Computer Configuration > Policies > Administrative Templates > Windows Components > Windows Update.
- Double-click the Windows Update Folder.
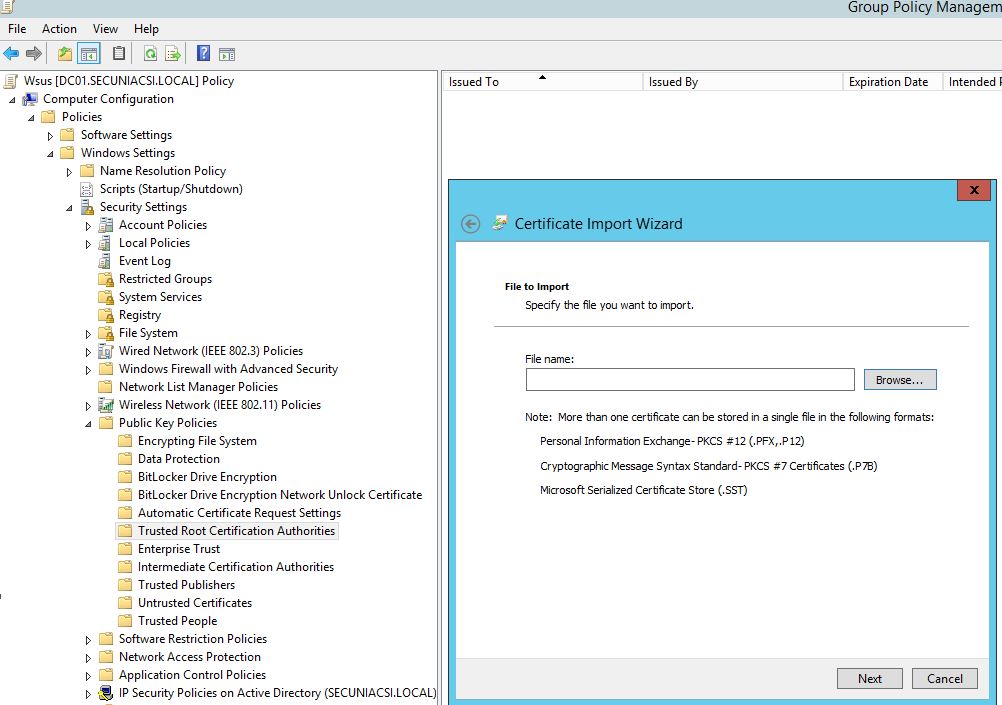
- Double-click "Specify Intranet Microsoft update service location" and change the Settings to Enabled (Please specify your WSUS server address on ''Set the intranet update service for detecting updates'' and apply (Note: This setting should only be changed if you are using WSUS. Don't configure this setting if you are using SCCM). If you have another GPO which points your machines to the correct WSUS server, then re-specifying WSUS is not required.
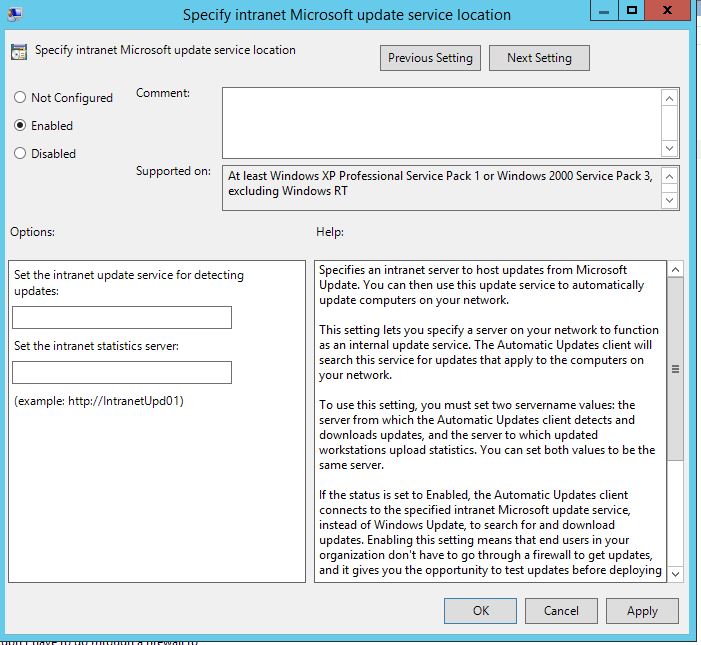
- Double-click "Allow signed updates from an intranet Microsoft update service location" and change the Settings to "Enabled".
- Click Apply > Ok and close the GPO editor.
Additional Information
Computers will download the Policy after the next policy refresh interval or reboot. You can force the policy to apply by running the command:
gpupdate /force
Sometimes it may take several hours for the policy to actually propagate. You can verify that the GPO is being applied to the machine by checking to see if the certs have been added to the appropriate cert stores on any given machine.
If the GPO has not been applied yet, or it is not being applied to the machine in question, then you will receive an error (0x800b0109) when deploying third-party updates.
on
Nov 16, 2018
04:45 PM
- edited on
Sep 16, 2019
03:29 PM
by
![]() RDanailov
RDanailov
